Why secrets management matters
Modern infrastructure depends heavily on secrets:
- API keys
- SSH keys
- database passwords
- access tokens
- cloud credentials
These secrets power:
- CI/CD pipelines
- automation workflows
- monitoring systems
- production applications
But in many environments, secrets are still stored in:
- shell scripts
.envfiles- Git repositories
- shared documents
- hardcoded application configs
This creates one of the biggest hidden risks in DevOps environments.
What is secrets management
Secrets management is the process of securely storing, accessing, rotating, and auditing sensitive credentials used by systems and applications.
The goal is simple:
Ensure the right system gets the right secret at the right time—without exposing it unnecessarily.
Common risks of poor secrets handling
Hardcoded credentials
Secrets embedded directly in code are difficult to rotate and easy to leak.
Shared credentials
Multiple systems using the same secret reduce accountability.
Long-lived secrets
Credentials that never expire become high-risk attack targets.
Poor access visibility
Teams often don’t know:
- who accessed a secret
- when it was used
- where it is stored
Principles of secure secrets management
Centralize secret storage
Avoid scattered credentials across infrastructure.
Use a centralized secrets platform instead.
Enforce least privilege
Applications should only access the secrets they actually need.
Rotate credentials regularly
Short-lived secrets reduce exposure.
Audit all access
Every secret retrieval should be logged and traceable.
Types of secrets commonly used in infrastructure
Infrastructure credentials
- SSH keys
- hypervisor credentials
- cloud access keys
Application secrets
- API tokens
- database passwords
- SMTP credentials
Automation credentials
- CI/CD deployment tokens
- n8n workflow credentials
- monitoring integrations
Secrets management approaches
Environment variables
Common but limited.
Pros:
- simple implementation
Cons:
- weak visibility
- difficult rotation
- exposure risk in logs or process lists
Encrypted configuration files
Secrets stored encrypted at rest.
Better than plain text, but still operationally complex.
Dedicated secrets management platforms
Centralized systems provide:
- access control
- auditing
- automatic rotation
- dynamic secret generation
This is the preferred enterprise approach.
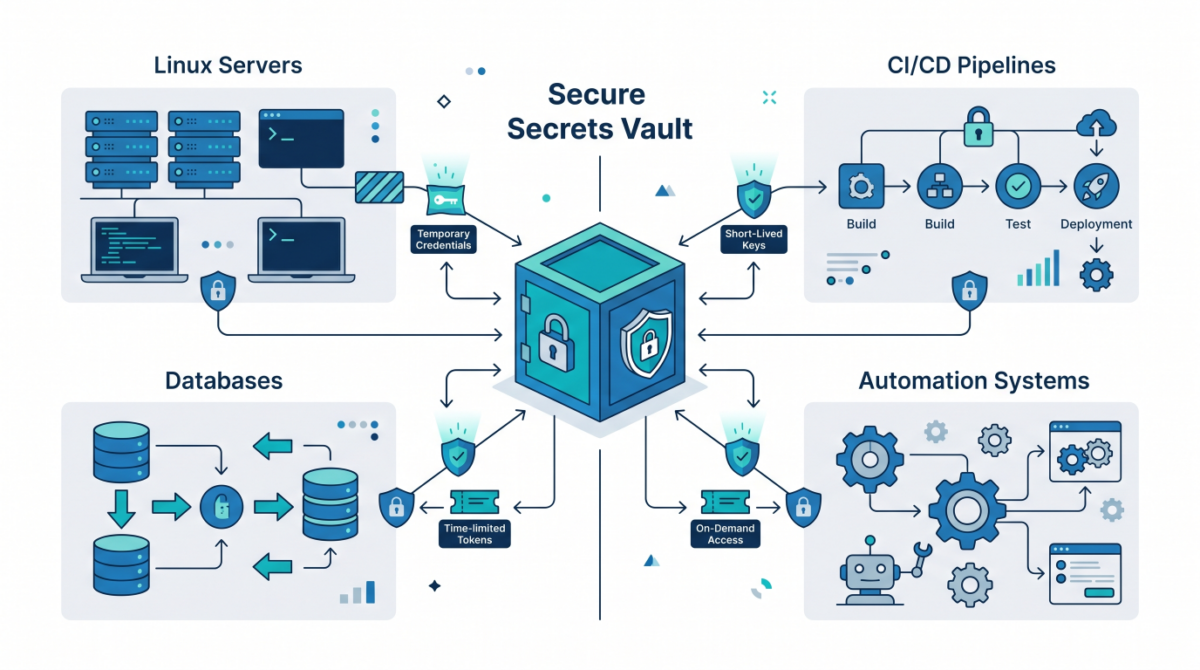
Dynamic secrets and temporary credentials
Why static credentials are risky
Permanent passwords often remain active for years.
Dynamic secrets model
Systems generate temporary credentials on demand.
Example:
Application → Authenticates → Receives short-lived DB credential → Credential expires automatically
Benefits:
- reduced attack window
- simplified rotation
- improved security posture
Secrets management in CI/CD pipelines
Avoid storing secrets directly in pipelines
Never hardcode credentials inside build scripts.
Use secure injection mechanisms
Secrets should be injected only at runtime.
Separate environments
Development and production secrets must remain isolated.
Secrets management with automation tools
n8n workflows
Each workflow should use:
- isolated credentials
- scoped permissions
- secure storage integrations
Infrastructure automation
Automation tools should retrieve secrets dynamically rather than storing them locally.
Linux infrastructure best practices
Restrict file permissions
Sensitive files should only be accessible to required users.
Avoid exposing secrets in logs
Sanitize outputs and debug messages.
Disable unnecessary shell history
Prevent accidental credential leakage.
Monitor secret access
Detect unusual credential usage patterns.
Example secrets workflow
- Application authenticates to secrets platform
- Identity is verified
- Temporary secret is generated
- Secret is used securely
- Credential automatically expires
No permanent password exposure is required.
Common mistakes to avoid
Storing secrets in Git
One of the most common and dangerous errors.
Reusing credentials
Compromising one system compromises multiple environments.
Ignoring rotation policies
Old credentials become long-term liabilities.
Overprivileged access
Applications should not access unrelated secrets.
Conclusion
Secrets management is no longer optional in modern infrastructure.
By implementing:
- centralized secret storage
- dynamic credentials
- least privilege access
- automated rotation
organizations can dramatically reduce credential-related security risks while improving operational control.